THE SIGNAL
This year’s numbers are genuinely alarming. We're tracking over 48,000 CVEs (Common Vulnerabilities and Exploitation) disclosed in 2025 alone. Attackers weaponize them in 5 days, while most organizations take 200 days to patch. The math doesn't work.
Then there's the AI problem. Nearly half of all AI-generated code contains security vulnerabilities. We're shipping faster and breaking more.
Meanwhile, the market has snapped into focus: 4.8 million unfilled cyber roles globally. The industry finally realized security isn't optional.
CVE PER YEAR
The vulnerability explosion is real
2025 is shattering records. In the first half of the year alone, we saw over 21,500 CVEs disclosed. That's 133 new vulnerabilities per day.
What's worse isn't the volume: it's the severity. Thirty-eight percent are rated High or Critical. Security teams can't just defer these. Over 8,000 high-risk flaws need attention immediately.
Artificial Intelligence
The AI paradox
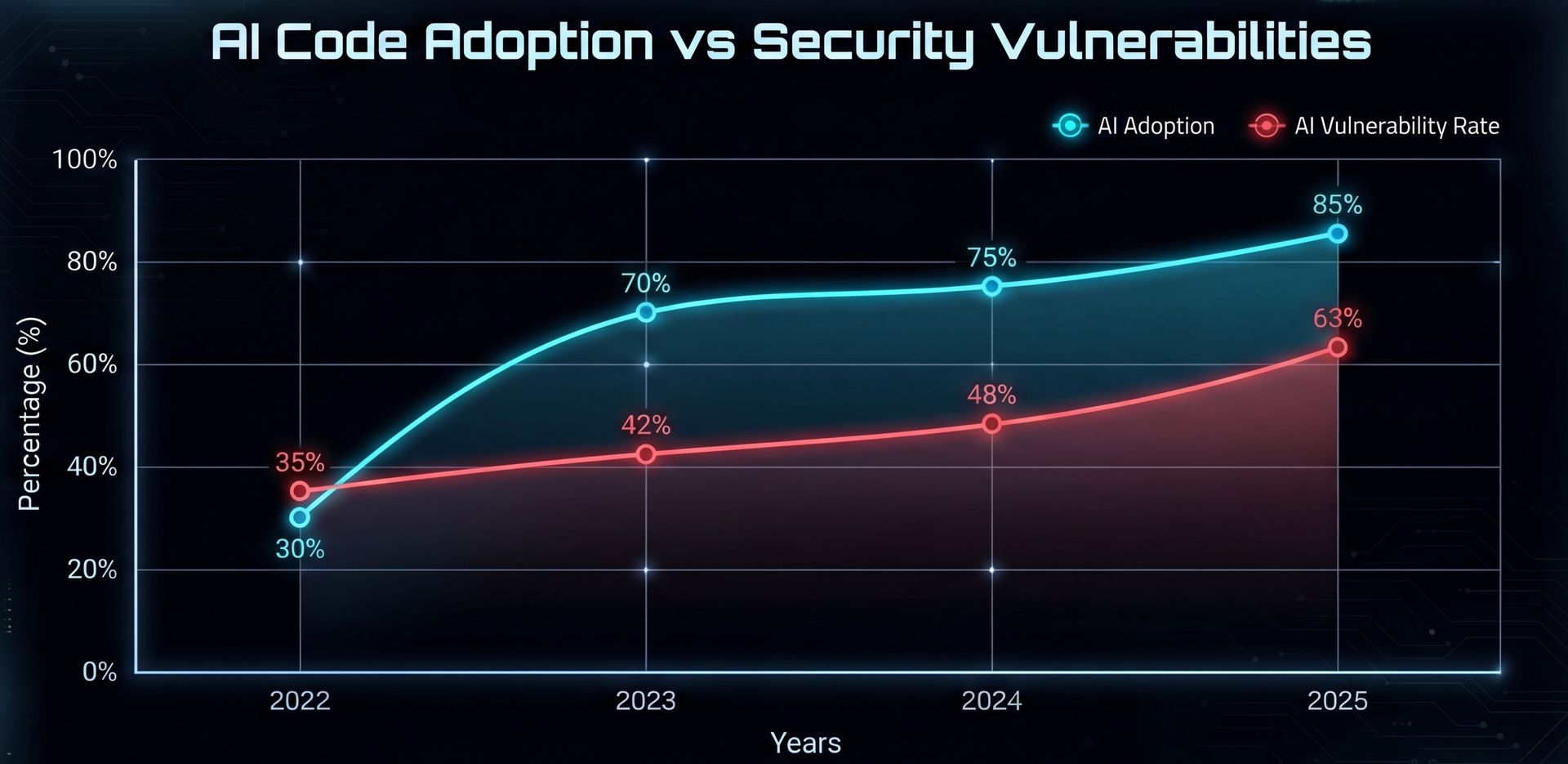
Why? LLMs train on public repos full of insecure code. SQL injection appears so frequently that models learn it as a "valid pattern" rather than a catastrophic flaw.
Even worse, each "refinement" iteration introduces new vulnerabilities. After just five iterations, you're looking at a 37.6% increase in critical flaws. We asked AI to help us write code faster. It delivered speed, but the security debt is compounding.
JOB MARKET
The speed gap that kills
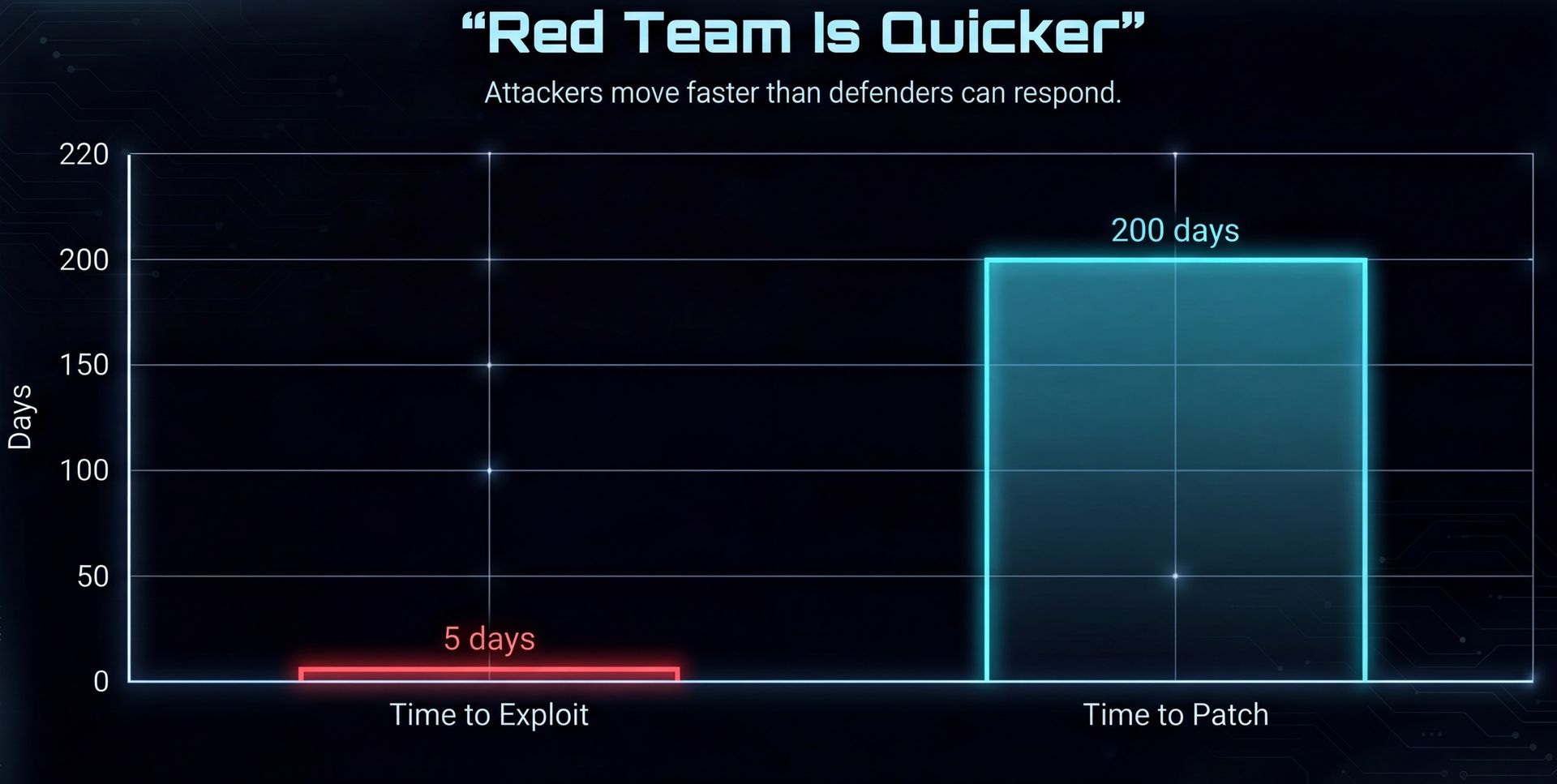
The timeline mismatch is brutal. Attackers exploit vulnerabilities in 5 days on average. Thirty-three percent are exploited within 24 hours.
Most organizations? They patch in around 200 days.
That's a 40-fold gap. By the time you apply a patch, the vulnerability has been exploitable for nearly 7 months. CISA mandates 15-day patching for federal agencies, but operationally, most organizations can't hit that. The math simply doesn't work.
CAREER
What this means for careers

I keep coming back to one number: 4.8 million unfilled cyber roles globally. The job market grew 12% this year while the rest of tech contracted.
A well-staffed security organization saves $1.76 million per breach compared to understaffed ones. That differential alone justifies premium salaries.
Specialized skills are where the real leverage is. AI security commands a 20-35% premium because almost no organization has built AI-specific security programs yet. Cloud security adds 15-25%. Incident response pops 10-20% during active crises.
Here's what gets me. A junior SOC analyst in 2025 has better job security than a junior software engineer. That's the inverse of the entire 2010s tech landscape.
The opportunity
This isn't hype. It's structural.
More code plus less secure code equals more vulnerabilities. More vulnerabilities plus slow patches create more breaches. More breaches combined with regulations means non-negotiable hiring. The talent shortage drives premium salaries.
The cycle feeds itself, and it's not slowing down.
If you're looking for leverage, cyber is where supply and demand diverge most sharply.
🛠️ The credentials that actually matter:
CISSP: The senior-level credential. Covers 8 domains across security architecture, risk management, and operations. Requires 5 years experience. Once you have it, you're in the room for budget and strategy decisions.
CISSP: Entry-level baseline. Covers network security, compliance, threats, and incident response. No experience required. The foot-in-the-door cert that gets you noticed.
OSCP: Hands-on offensive security. You get 24 hours to breach 5 machines in a lab exam, no multiple choice, just actual hacking. The proof that you can pwn, not just talk about it.
THE PLAY
I've been thinking about this a lot. If I were pivoting into security today, here's what I'd do.
Start with Security+. It's the baseline credential that gets your foot in the door.
Build a home lab. TryHackMe or HackTheBox. Actually practice against vulnerable systems, you can't learn this from books alone.
Start doing bug bounties. HackerOne, Intigriti, wherever. Real targets, real feedback, maybe even real money.
The timeline is 6-12 months from zero to employable. But the ROI compounds. AI security is frontier territory - almost no one has built programs here yet. That's the gap.
Until next week,
@speedy_devv